In early January of 2021, Mary Fanning and Alan Jones published two pieces in The American Report entitled:
Proof Positive: Coordinated Cyberwarfare Attack Against US By China, Russia, Iran, Iraq, Pakistan To Steal Election From Trump
and
STEALING AMERICA: ‘Former’ Communist Comey Got SCORECARD Election Hacking Source Code, And Knew SolarWinds Was Not Secure
These articles claim to have positive proof of a massive coordinated international cyber-attack against multiple US election sites during the first week of November 2020. The stated aim of this attack was allegedly to steal the election from Trump. The authors of these articles claim that two secret tools were used in the attack: one called “Hammer” and the second called “Scorecard”. The source of this highly secretive information was a mysterious and ‘well-connected’ individual by the name of Dennis Montgomery.
The American Report articles came with a large number of supporting data sets and animated charts (the same material was also used in Mike Lindell’s movie “Absolute Proof”) that purports to show the details of these cyber-attacks. The data includes source and target IP and MAC addresses, the method of infiltration, and the vote count changes to several voting systems. All in all, it seems like a real smoking gun and the stuff that cyber unicorn dreams are made of.
I wasn’t aware of this claim until a friend asked me to look it over. It didn’t take long to reach the conclusion that the Montgomery data referenced in the two articles and in Lindell’s movie is a crude fabrication and is a forgery.
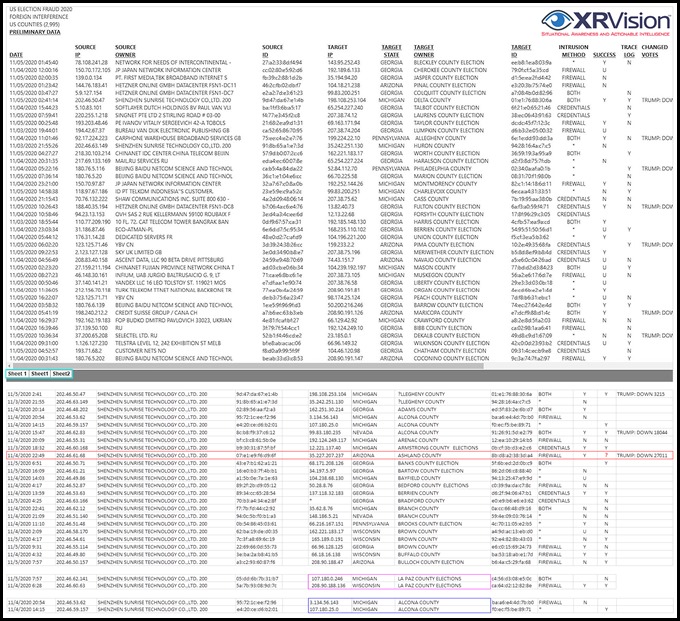
Image 1: Sample data anomalies: (1) A source for the alleged attack, an entity called “SHENZHEN SUNRISE TECHNOLOGY CO.,LTD. 200”, is a Shenzhen/Hong Kong-based company, but instead of providing a specific IP address with a building, floor, and room # location of the machine which is allegedly launching the attack, it lists 157 generic company IP addresses. (2) The “LA PAZ COUNTY ELECTIONS,” which is in Arizona, shows up in two different states (Michigan and Wisconsin) with two different IP addresses. (3) The IP address of the Michigan Alcona county target is both 3.134.56.143 (Columbus, Ohio) and 107.180.25.0 (Ashburn, Virginia)
Even basic analytics on Montgomery’s data show that it’s laced with errors and anomalies. Here are a few examples:
- Many of the source and destination IP addresses don’t match the geolocations specified
- Some of the company/entity names don’t match the assigned locations (e.g., a company identified in Beijing, China, is actually located in Hong Kong)
- The “SOURCE OWNER” column uses DBA names for companies instead of the actual legal name, which is what you would get if you did a low-level IP to organization resolution (a mandatory step for the intelligence to be actionable)
- All of the destinations are protected with firewalls, so the “INTRUSION METHOD” reference to the word “FIREWALL” is meaningless. From the limited attack vocabulary used in the document, it’s obvious that whoever wrote this isn’t familiar with actual cyber-offensive operations.
- The DATE column is missing time zone information. The repeating distribution pattern of date-time stamps also strongly suggests that they are non-organic and instead were produced using some cyclic function with a random number generator.
- Some of the records are incomplete. For example, one row in the “CHANGED VOTES” column states “TRUMP: DOWN 44,905”, but it failed to add the “Y” under the corresponding “SUCCESS” column.
- The tabs on the spreadsheet show that the titles were created manually (“Sheet 1” vs. “Sheet1” missing the space), which is unlikely if this data came from an automated process.
- The values in the fields titled “SOURCE ID” and “TARGET ID,” which have a MAC address format, were most likely created with a random number generator. A sampling of these addresses yielded no results of known network card manufacturers.
As for Dennis Montgomery, the source behind this high-value intelligence, he is a certified lifelong con man and a felon with a long rap sheet of scams. As Ecclesiastes 1:9 observes, there is nothing new under the sun, and it turns out that Montgomery’s latest con is almost identical to several others he pulled off over the years on targets such as Sheriff Joe Arpaio, the DoD, CIA, various LEAs, and the DOJ. One noteworthy case in Montgomery’s illustrious criminal portfolio is the 2010 six felony charge for writing a bad ~ $1M check in 2008 to a Vegas casino. This case provides the strongest indication that Montgomery is a managed asset, as the case remained in limbo for 12 years, with the court failing to sentence him. I’m not a betting man, but if I were, I would place all of my chips, and the case would get dismissed once the current op is rolled up.
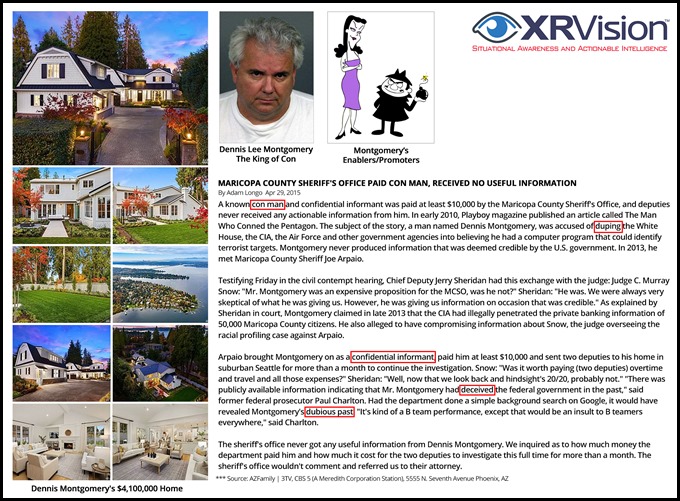
Image 2: The profile of Dennis Montgomery, the king of con
It’s not entirely clear who paid Montgomery to create/promote this fabrication. Motivation-wise, it could be just another money-making grift. Still, it’s more likely that this is a well-organized and funded Romney/Bush operation that is designed to kill any discussion about actual election fraud and discredit President Trump.
As for his chief promoters, Mary Fanning and Alan Jones, a cursory evaluation of their body of work shows no verified intelligence and a large number of high-grade/high-volume disinformation operations. Here is one example (and don’t worry—you don’t need top-secret US government clearance and years of intelligence training to view/understand it).
In a January 14, 2021 tweet entitled “PRO RUSSIAN LDNR OPERATIVE WITH ANTIFA AT THE CAPITAL BUILDING,” Fanning positively identified an Antifa and a Russian operator at the Capital riots. This post illustrates her MO: a continued spray of tiny bits of truth in a sea of deception, also known as the firehose of falsehoods.

Image 3: Mary Fanning (using the moniker @realMaryFanning misidentifying the political affiliation of Dybynyn as pro-Russian
The individual depicted in Mary Fanning’s image standing next to the horned Viking (an actor that goes by the name of Jake Angeli, AKA Jacob Anthony Chansley, who has no public ties to Antifa) is indeed Sergai Dybynyn. Still, the classification of his political and operational linkage is wrong. Dybynyn is affiliated with members of the Ukrainian nationalist movement, some of which openly embrace extreme right-wing and fascist ideologies. Fanning’s arrest warrant source claim for Dybynyn is also wrong; it wasn’t issued by the “Ukrainian Ministry of Interior” but rather by the Pro-Russian separatist: “DSP of the Ministry of Internal Affairs of the LPR (Lugansk People’s Republic).”

Image 4: Disinformation in its purest form and its sources. The actual identity of Sergai Dybynyn, who Mary Fanning misidentified during the Capital riots as “pro-Russian” and his arrest warrant by the Lugansk People’s Republic. Before you start screaming that the “Zhidobanderite” image on Ihor Kolomoysky’s T-shirt was photoshopped, chill, this alliance/marriage of convenience with the ideology of the Právyi Séktor is well documented.

Image 5: A deeper dive into Dybynyn and three other related individuals wanted in the LPR arrest warrants. All four are Ukrainian nationalists. Roman Bochkala, one of the wanted men, is a US Peace Corps volunteer in Ukraine who visits the US regularly and has attended training in the US (via the Open World program). Interestingly, he also seems to be a frequent flyer on various US military aircraft. If you are still not convinced about what these people think about the Russians, check the message on Roman’s right-hand bandage.
My advice to anyone reading The American Report and contemplating swallowing the Montgomery forgeries or other Q-Anon sleeping pills is to be aware of false prophets. They come to you in sheep’s clothing, but inwardly, they are ravenous wolves.
If you want to investigate/prove possible election fraud, you don’t need hush-hush data that purports to come from ‘secret leaked’ NSA/CIA projects or anonymous individuals. Just focus on factual, legally obtained evidence to stand up in court. For example, official CCTV footage with chain of custody verification shows identifiable vehicles delivering dozens of ballot boxes in the wee hours of the night. Scanning the same ballots multiple times without supervision and the resulting one-sided statistical vote anomalies should tell you something. If you claim to have seen ballots being trafficked/shredded/burned, produce the actual evidence, images of traffickers can be easily identified and shredded ballots can be easily reassembled. If you suspect voting machine irregularities in a specific race, conduct a manual recount of the paper ballots and compare it to the voting machine count. Don’t accept any fantastic explanations about Delta force raids in Germany or votes being transmitted/manipulated overseas via military satellites. This is all disinformation that is designed to destroy the credibility of actual voting fraud investigations, and it’s coming from the same ‘patriotic’ republican establishment sources that produced Q-Anon and the Italian Job.
If you don’t like what you see around you and want to change it, don’t wait for the ‘good guys’ to do it for you. There are no good guys out there. JFK Jr. is not returning to save us, and you certainly shouldn’t trust Sessions or Barr. Instead, get personally involved and hold your representatives accountable at the ballot. Here is a simple litmus test: disregard what politicians say about foreign, economic, immigration, and other policies. Instead, focus on one thing only: the complete breakup of big tech and SM monopolies like Microsoft, Google, Amazon, Facebook, and Twitter. This should be the only priority for the next election cycle. Any politician who didn’t/doesn’t actively work for their breakup and continues to support their Section 230 protection should be voted out of office.
*** Update 02/21/2021 ***
Jeff Nyquist, who was Mary Fanning’s source for Dybynyn’s identification as a Russian operator at the capital claim has begrudgingly updated his post to reflect Dybnynin’s actual political affiliation.
*** Update 08/29/2022***
After 14 years in limbo, the case involving six felony charges against Dennis Montgomery has been dismissed.
References and Sources
Audio 1: Excerpt of a 2017 Mike Zullo interview with Dennis Montgomery. Most of the claims made by Montgomery during the interview show a complete ignorance of cybersecurity tradecraft and practices.
Document 1: Dennis Montgomery’s Foreign Election Cyber Attack Data Set
Dennis Montgomery in a nutshell
Montgomery allegedly sexually assaulting one of his female employees
An FBI 302 detailing Montgomery’s IP and equipment theft from his former employer, eTreppid
Document 2: A profile of DOJ asset? Montgomery’s indictment and conviction for 6 felonies from 2008 is still open as of September 14, 2020.

Video 1: Content promoted by Mary Fanning. January 7, 2021, The Ukrainian Information Agency (UNIAN) and the Glavred (1plus1) TV station disinformation publications falsely identifying Russian supporters of President Trump storming the Capitol building

Video 2: Assault on Donetsk Airport – A 2014, pro-Ukrainian war footage produced by the dynamic duo Sergai Dybynyn (cameramen) and Ruslan Smeshuk (reporter)
Copyright 2021 Yaacov Apelbaum, All Rights Reserved.
This looks like the same information that Mike Lindell was relying on. I hope he didn’t get burned.
Regardless of what is being said about Dennis Montgomery, in my opinion, he couldn’t be any more of a liar and criminal than people in the FBI and DOJ. The things that they do to innocent people is horrendous. They re masters at setting people up and destroying them. They have all the money in the world and the might of the U.S. Government. It is a crime what they do to some innocent people.
Further, the cyber warfare analysts who leaked the video graphics in real time while the Chinese and other countries, including the UK, Italy (an Italian employee working for Leonardo confessed), Iran, Germany, Pakistan, and . . ., were switching votes from Trump to Biden in the wee hours of 11.4.20. The proof is there. Go look at it. The graphics illustrating the steal was made by the U.S. Military and civilian experts in cyber warfare. (Ref. Mike Lindell’s “Absolute Proof” and fast forward to the last 20 minutes. Please watch. Forget about Hammer and Scorecard. The election was stolen. You can watch it happening real time.)
Hi Melinda,
A few comments about your observations.
None of the data presented by Marry Fanning was captured in real-time. If this information is genuine (which I don’t believe it is), it would have at best been captured in “near-real-time” or post event. By “cyber warfare analysts who leaked the video graphics in real time” are you referring to Dennis Montgomery or is there another source for this data? The only graphics presented in the movie are the alleged source and destination traffic patterns projected on a map. These graphics are just visualizations of the same data.
If you want to find potential election fraud or irregularities, you don’t need to take more QAnon style sleeping pills– which is likely the engine behind claims such as “Italian employee working for Leonardo confessed” and leaky white hat cyber warfare analysts who work around the clock do defend us from evil. Instead, demand manual re-count for contested races and compare them to the voting machine counts. Or, concentrate on factual cyber evidence that can stand-up in court. Like for example: official CCTV footage showing multiple scans the same ballots, ballot traffickers, etc.
I suspected as much and agree with this assessment. It does discredit the truth when real (or fake) TRUTH SEEKERS stoop to the level of the fraudmasters they seek to discredit. It just creates more noise and cognitive dissonance.
Montgomery is a con man, he doesn’t lift a finger unless he can make some money in the process. But his patron/handler was probably more interested in the cognitive dissonance effect.
This is unfortunate, as I have seen many linking to this data. As a result, real data is being disregard. Yaacov, I know this is a very general question, but can you do an article on some of the most legitimate cases of fraud?
Two potential sites for investigation are Fulton County, Georgia and the TCF Center in Michigan. But, keep in mind that the issue with any investigation is that you need access evidence such as: logs, CCTV footage, names/images of the individuals/vehicles etc. This has been very difficult to get. Even in the case of the TCF center, it has been an uphill FOIA battle.
The issue with the voting machines is even more complex, because the only real way to verify their accuracy is to conduct a manual verification count and compare it to the software output. This is a simple task, but I’m not sure how to compel the various election boards to agree to provide the ballots. Just like with any QA/QC problem, it’s more of an oversight issue than technology.
Is this you? https://en.wikipedia.org/wiki/Jacob_Appelbaum
Thanks!
Noop, no relation beyond both names originally meaning apple tree in German.
Right now, I am spoofing my IP from PA and it appears to be from Australia. Your premise forgets the in CYBER WARFARE, you can’t trust the IP Address, it is easily spoofed. Frankly, you can also spoof the sources name. The point is the Voting Machines are on the internet, and they can be hacked by a voter in 30 seconds. That is reality.
Yaacov, I truly enjoy reading all of your gathered information. I know you take a lot of time to carefully gather and examine your findings.
I have seen this information you displayed today. I never looked closely at it bc cyber traffic baffles me and I could not find any validity to these documents. So with that said, Thank you for clarifying this portion.
I wonder if this is information that Sidney Powell had gathered and relied heavily on as evidence to election fraud.
I do know there was election fraud. I am dumbfounded that we cannot produce absolute proof, or perhaps there is such but we are not apprised of that information
Meanwhile. Here we are.
What a revolting state of affairs we are enduring.
The left is just evil
I am not sure what information Sidney Powell has collected and what her sources are. In general, her team seems to have challenges with vetting sources and collecting quality evidence. The same applies to the Trump administration, which for some reason, had struggled with situational awareness for the entire four years.
Proving fraud in court is a challenging task on any case, even more so on political cases when there is so much at stake. I’m not sure we have a true left (i.e a true Marxist movement) in our country, I think it’s more of a hybrid effort of the old Bush Sr. republication guard and the Red-Greens-Black coalition. For example, a lot of the QAnon style content is coming form Republican sources affiliated with traditional Republicans like Mitch McConnell and John McCain (e.g. the Lincoln Project).
The Red-Green Alliance and the Real Devil of Mogadishu
Toxic Masculinity My Foot!
The Fifth Column and the Pro-Iran Movement in the US
Jim’ale The Jihadi Organ Grinder and his Little Tweeting Monkey
Yaacov, I have been an election worker in my TN county for 20 yrs, the last 8 appointed to the Absentee Counting Board, so now it’s been two Presidential elections that I’ve worked on in that capacity. Our state Supreme Court this past summer (2020) did not permit additional reasons for people to request Absentee Ballots, so the excuse of being afraid to be exposed to COVID-19 by voting in person did not stand, especially as there is multiple opportunities for early voting and that you no longer need to vote in your precinct, but rather at voting stations throughout the county during early and Election Day voting. There was strict enforcement of social distancing and mask-wearing at these stations. The result was a surge in Absentee Voting, which I saw on November 3. Because of the increased requests for the ballots, the Board of Elections nearly tripled the number of workers to count these.
We start by making a record sheet of each precinct’s vote tally according to Bd of E records; then open the envelopes sorted by precincts, remove affidavit envelope with ballot inside; separate affidavit (signed) tab from the envelope that contains the ballot; check that ballot is from the right precinct that we are counting (stamped on bottom by Bd of E when it is sent out to voter); if it isn’t we take it to where that precinct count is taking place. The ballot is now truly secret — no way to see any i.d. on it except for its home precinct. Remember, the Board of Elections knows how many absentee requests they fulfilled; some of them may not have been returned. So the numbers have to balance before we even start running the ballot cards through the scanners. The scanners do not tell the results except to say how many ballot cards you entered for that precinct. So if you could do this, you could compare the number of affidavit tabs with the number of ballot cards for a given precinct. These should be the same #, although occasionally some fool forgets to put his/her ballot card into the envelope! Yes!! We don’t need those guys voting, do we?
I don’t have the figures at hand, but there were lots of new faces working — so many that we were done counting and entering into the scanners by 5:30 PM. The polls don’t close until 7 PM, so we sat there and waited! The few ballots that had been delivered by mail, UPS or FedEx (yes, people do this!) late in the day, NOT dropped off in person, were counted at hq and added to our total, which is then added to the totals of the machines at the various Election Day voting stations around the county which close down at 7:00 PM CST. Absentee, early voting and Election Day results then are totaled at the Bd of E and are reported, county by county, to the state which then calls the winners. TN went solidly for Republicans, but that was expected. Trump didn’t even campaign here that I know of, but we did have a primary battle for US Senate seat to replace “retiring” Lamar Alexander.
My suggestion to try and track what actually happened in November would be to see the county in the state you are “wondering about”s results for the election, obviously for President, but then see if the totals for US Senate, Congress and down the line match up. Lots more Democrats voted Absentee than has been my experience in past elections, because they did NOT have the option in TN to do the mail-in thing, which was used in other states to load up the Biden-Harris results but MAYBE not so much the down-ballot vote, especially if they were just grinding these out quickly on someone’s kitchen table. Voting information sheets that are sent with absentee ballots can be very confusing as there could be local issues in one precinct, but not in a neighboring one, so if a ballot is marked incorrectly that would be a problem. There maybe strong clues here. Even looking at next-day election results in local newspapers may be very telling if you see big discrepancies in the results of various races. There could be clues without too much digging needed. Sorry to be so long in relating this procedure. Best wishes!
Thank you for the detailed explanation. It’s very informative. I think one simple but effective strategy would be to use a manual count in high contention races. If the manual count ends-up matching the machines counts (plus minus some acceptable variations), then there should be no issue and we can safely put this claim to rest. But, if it doesn’t, it should open the door to a complete forensic evaluation of all of the voting machines country-wide.
In video analytics (i.e. face recognition, LPR, OCR, etc.), we use a concept called a ground truth. This is an actual manual count of events that includes false, true, and missed detection. Only after you conduct this detailed count, you can estimate the precision of your video analytics. Without it, there is no way to tell how accurate you really are. The same applies to vote scanning machines which are simple OCR devices.
Sothis guy just get away with this all the time? I’m sure yaacovs tribe is behind it. Through deception we will wage war – mossad.
Thank you for your comment Americ. From the poor grammar it looks like despite your assumed name you are not from around here. I also have the burning suspicion that you are not a real biblical scholar.
Two comments:
1. Not sure I get your comment about my ‘tribe is behind it’ — The only tribes in the US are the native Americans, and the last time I checked, I wasn’t a member of any of them.
2. Your quote “Through deception we will wage war” is incorrect, the actual phrase comes from Proverbs 24:6 and is: “For by wise counsel thou shalt make thy war”. At any rate, the official motto of the Mossad is: Proverbs 11:14 “Where no counsel is, the people fall, but in the multitude of counselors there is safety.”
Yes, Mr. Americ, this may sound a bit pedantic, but, “Der liebe Gott steckt im detail”. If you are seriously considering a career as Pakistani anti-semitic provocateur, and want to be taken seriously, you will have to pay more attention to detail.
We are told that the Dominion machine (arbitration) logs in Antrim County (Michigan) have been deleted. That is going to be our starting point for uncovering fraud. If, for any reason, they cannot produce those logs, all hell will break loose. IT MUST.
Mike Lindell should not have gotten involved with his sloppy presentation. The left are truly masters at disinformation. They used Q anon to divert the dummies now call Qtards, inserted AG to us unsuspecting patriots at events. Then there were the dumb MAGA people who followed the AG groups to the White House. I’m sure Trump regrets being there on Jan 6. Those groups like the boogaloo bios and oath keepers or whatever there names are have AG people to ruin the MAGA or America First Movement.
Thank you for all your analyses
Yup, I agree,
Many of the QAnon style organizations are in fact domestic influence operations (at least at the leadership level). Also, a lot of what we’ve seen over the past 4 years in terms of ‘camera facing’ right-wing violence and anti-semitic iconography comes from a well-organized and financed progressive influence campaigns.
The Anti-Defamation League Must Go
Need a Nazi for a Project, but Can’t Find One? Here’s How to Make One Up
https://apelbaum.files.wordpress.com/2021/02/enrique-tarrio-2.jpg
Hi sir, i assume your comments are based on the entire xl doc. Or is it just these two pages? Maybe I missed your link. If not, can you post a link to the entire fanning doc? We’d all like to have a look. Thanks for your efforts. Best!
The analysis was done on a number of documents, here is one of the spreadsheets (it has two tabs):
https://apelbaum.files.wordpress.com/2021/02/cyber-attack-data-1.xlsx
You do not know if this is the same spreadsheet or information Lindell or Powell is using. This could simply be more deep state disinformation. I would hope that Lindell and Powell did their due diligence. Let’s find out. Lindell claims his data is verified and correlates with real time observations.
How do you know this is Mike Lindell’s data? The article doesn’t say that!
Here is the linkage that ties Mary Fanning to the Dennis Montgomery material. My personal take on this is the Dennis likely coned Lindell and Fanning.
In Lindell’s case, he is a big-hearted guy that is trying to do the right thing. Fanning on the other hand, sells herself as an expert inelegance analyst, what’s her excuse for not vetting the data?
https://apelbaum.files.wordpress.com/2021/02/mike-lindell-using-mary-fannings-materials-1.jpg
Warning: Technical Jargon
The ID, or as it is technically known as an “Ethernet interface MAC address”, referenced in the evidence provided is complete BS. In a switched network, the MAC address is swapped out at every hop along the way. Unless the people that provided this info hacked into every single network listed and worked their way backwards to the source IP, there’s no way these MACs provided are valid.
Anyone that knows networking will see this immediately. As soon as I saw this “ID” column, I knew it was BS. This kind of crap makes valid inquiries and legit evidence collected look suspect.
Yup, I agree. It seems that the objective of the fabrication wasn’t to survive a close scrutiny (It’s not difficult to forge a realistic attack log), but to generate a document that is plausible enough to either jump start and influence operation.
Somehow my question was erased. Can you link to all of the pages in the fanning doc? Thanks!
Here is the link to the spreadsheet:
https://apelbaum.files.wordpress.com/2021/02/cyber-attack-data-1.xlsx
Waiting for defamation rebbuke from china if its really bullshit
It is certainly disappointing if this attempt to illustrate the causes of the stolen election are in fact a fraud, but the fact remains the election was a fraud. Even ignoring every other thing which PROBABLY happened, the simple dis-enforcement of election laws (an established FACT acknowledged by those States) in the swing States certainly tipped the election.
This is analogous to the fake Hillary PizzaGate video the left put out to discredit the real video.
Roger that.
Joe Biden OPENLY ADMITTED THE BELOW :
On October 24th, 2020, Joe Biden stated: Nobody has to vote for me for me to win , we have put together the most extensive and inclusive voter fraud organization in the history of American politics.” Whether he meant to say it or not, he confessed to what most conservatives already know: the undeniable reality of Democratic election theft.
Yeah, it could have been a Freudian slip-and-fall, but, considering the fact that he is showing clear signs of cognitive decline he could have unintentionally dropped the word “anti”. As in ‘anti’-voter fraud organization.
Regardless of the word “anti”, the first part of his statement is the reveal,… “Nobody has to vote for me for me to win,…..”.
Reading the statement with or without “anti” doesn’t change the first part in any way.
Maybe, but again, you are dealing with an individual that is exhibiting advanced signs of cognitive decline. Just the mere fact that he said that in public is a ‘slip’.
Thank you for sharing this. There has actually been an intrepid Sheriff, Detective and
News Editor and who have been leading the way on this story. The sad thing is that nobody has ever
bothered to share this truth, but I will and may it “take root downward bearing fruit upward”.
Telling the truth can get you silenced, which is what has happened to Sheriff Arpaio, Detective Michael Zullo and Sharon Rondeau News Editor of ThePost&Email and a good number of others that have shown courage, honor and integrity in this story. The King James Holy Bible is filled with many names that gave it all to tell and live for the truth or Foxe’s Book of Martyrs.
No less than the prior three administrations to President Donald John Trump’s, and most specifically the one who spied on President Trump, Barry Barack “Haman” Hussein Soetoro have projected their guilt, shame and criminality onto the people of America and have used President Trump as their number one target in an attempt to take the people and nation straight to hell. (Matthew 16:18KJB; Psalm 35:7,8KJB)
The election fraud that led to what we are enduring at this very moment can be laid at the feet of a cowardly complicit congress, courts, and communist media covering up the lie of Barack Hussein Obama not being a natural born American citizen,(Article II Section I Clause V presidential eligibility requirement) and then attempted to cover up this truth with the forensically proven fake, fraud and phony baloney birth certificate and selective service registration draft card. This was proven after tireless and honorable work by Sheriff Joseph M. Arpaio, Detective Michael Zullo and the Cold Case Posse.
Anybody who ever spoke the truth about this has had the gates of hell come against them, but in Christ Jesus the Lord those gates of unholy hell shall not prevail, but shall take the unrepentant unregenerate in their very own evil schemes, plots, plans, and devices.
Telling the truth or asking real questions can get you banned and labeled you guessed it, a conspiracy theorist. This false label was implemented by none other than the cia when President Kennedy was murdered.
I direct you to the firsthand source of this story with two recent stories that will help bring this all into better context. https://www.thepostemail.com/2021/02/11/hammer-hoaxer-infiltrates-lindells-absolute-proof-2/
Also you can find Sheriff Arpaio’s honorable work here regarding his 5 year investigation that was mocked, slandered and hated, but loved by those who care to know and share this truth. http://wheresobamasbirthcertificate.com/
Once people accept this truth, we can start the healing process the nation and people in the world so desperately need from the Lord.
“Oh let the wickedness of the wicked come to an end; but establish the just: for the righteous God trieth the hearts and reins. My defence is of God, which saveth the upright in heart. God judgeth the righteous, and God is angry with the wicked every day.” Psalm 7:9-11 KJB
“The wicked is snared by the transgression of his lips: but the just shall come out of trouble.” Proverbs 12:13 KJB
Thank you for your comment Michael. Joshua 1:9
I have never heard of Montgomery and really don’t care about him or his role in this article. The election was stolen and the votes that were pumped into the election in the wee hours of the morning after battleground states all miraculously stopped counting (except for the videos that show them loading fake ballots) for the same amount of time while the record-setting Biden votes were received and loaded will not go away. The electonw as stolen with the help of our CIA and FBI and many republicans.
It’s clowns all the way down.
Nice work as usual.
Did Detroit have an over vote? Meaning more votes than registered voters.
Sorry, I don’t have/know any of the voting stats.
Right now, I am spoofing my IP from PA and it appears to be from Australia. Your premise forgets the in CYBER WARFARE, you can’t trust the IP Address, it is easily spoofed. Frankly, you can also spoof the sources name. The point is the Voting Machines are on the internet, and they can be hacked by a voter in 30 seconds. That is reality.
Thank you for your comment Mr. Weymouth,
1. Your IP address resolves to Santa Clara, CA, not Australia, but that’s beside the point. Montgomery claims to have resolved the sources of the attack to the MAC address level. So, there is no spoofing claim here. But, even if there was, the target IP/MAC addresses are still wrong.
2. Yes, using Proxy services like TOR is a common practice in cyber operations. But, I’m not sure if this is relevant to Montgomery’s dataset. Almost all of the information in his dataset fails to reconcile. This includes: duplicate geolocations with different IP addresses, the names/location of the organizations associated with the source IP, the target IP and MAC addresses, the MAC addresses themselves, the infantile description of the method of intrusion, etc.
3. Just because the voting machines had a network card/cellular modem doesn’t mean they were on-line at all times. How do you know for a fact that all of the voting machines were on the Internet at the time of the alleged breach?
4. I’m not sure I understand what “Voting Machines are on the internet, and they can be hacked by a voter in 30 seconds.” means. What is a machine on the Internet? Do you mean networked and with public access? Also, I’m not entirely clear on how a voter can hack a machine in 30 seconds? Contrary to what you see in movies, very few hacks take 30 seconds.
Finally, to suggest that this was a world-wide distributed hack by one entity is one thing, but to claim that this was a coordinated effort by Russia, Pakistan, Iran, Germany, Italy, and UK is bordering on the absurd. Why in the world would the Chinese government executed a cyber attack against the US from hundreds of computers that are based in China?
Why no more posts???
Did they get to you???
So much has and is going on and not a pep from you.
Busy at work :-)
I hope your working to expose our fascist government.
Same conclusions I came to, seems like months ago. Trump was re-elected. Sane people don’t want the insanity that the left is selling. It really needs to be no more complicated than that. But we have this not so great reset (great for elites, shit for plebes), and Trump was in the way of that.
Now, Gates can go it alone, with Herr Schwab, like all evil masterminds. There is no Melinda for Locutus of BORG.
Enjoy the vaccine virtue signaling my transhumanist friends. You not only eat GMO’s but now you are one.
I enjoy/appreciate the site and am just checking back for new content.
are you able to confirm the veracity of the tweet purportedly sent by Bgate, On January 12, 2020, Bill Gates sent out the following Tweet: One of the benefits of being 65… There is a photo appended to the tweet showing him taking the covid vax. Thank you
Noop, not unless you have access to the direct account and the source image.
This should come as no surprise:
source: https://www.washingtontimes.com/news/2021/aug/11/mike-lindells-lead-cyber-expert-says-they-cant-pro/
When it comes time to put up or shut up, Montgomery suddenly claims he had a stroke. And his data turns out to be, as you reported months ago, pure garbage.
The “Stroke” is an old Montgomery trick. FYI, that’s how in the past, he avoided showing for court/depositions.
Thank God for this article. Since then a cybersymposium was held based on this data. Lindell (a swindled patriot) also invited Q himself (Ron Watkins and his father larping to drive traffic to their depraved sites). Keep up the great work!
Thank you for your kind words. FYI, neither Ron Watkins nor his dad Jim Watkins are Q. They just hosted some of the Q content, neither one authored any of it.
I defer to your more excellent sources. My conclusions come from HBO’s Q:Into the Storm and that Ron’s Telegram posts look very much something “Q” wrote. Love your site!
Thank you for the kind words.